AI-Powered Security Breach

Introduction to AI-Powered Security Breach
You face a new threat in cybersecurity: AI-powered security breaches. Recently, Google stopped a zero-day hack developed with AI. This incident highlights the double-edged sword of AI in cybersecurity.
Understanding Zero-Day Exploits
A zero-day exploit is a vulnerability in software that is unknown to the vendor and has not been patched. You can use AI to develop zero-day exploits, making them more sophisticated and difficult to detect.
And the recent incident involving Google is a prime example. According to a report from Google Threat Intelligence Group (GTIG), prominent cyber crime threat actors were planning to use the vulnerability for a mass exploitation event.
The Role of AI in Cybersecurity
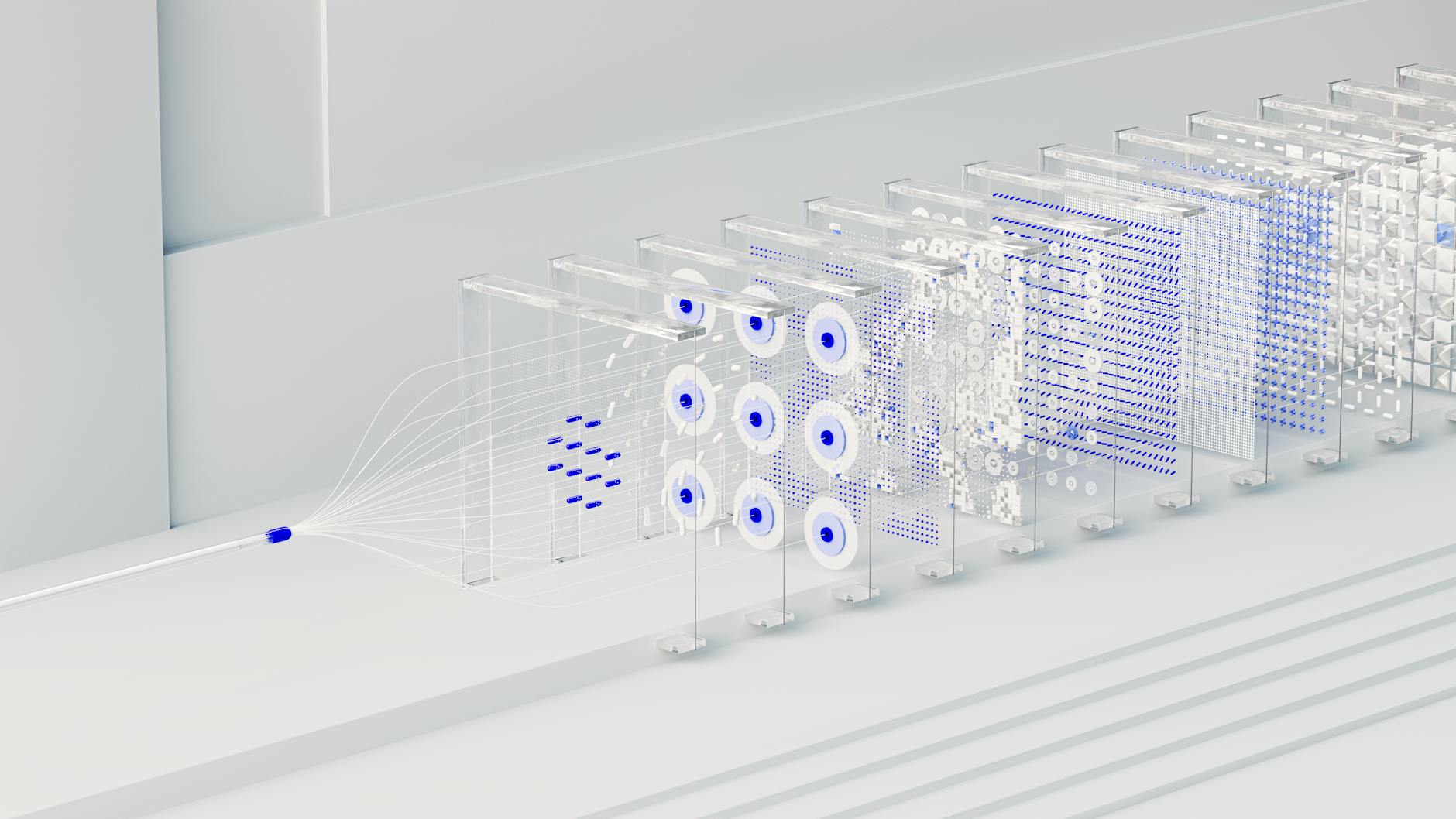
But AI is not just used for malicious purposes. You can also use it to improve cybersecurity. For instance, AI-powered systems can detect and respond to security threats in real-time, reducing the risk of a security breach.
So, what does this mean for the future of security? You need to be aware of the potential risks and benefits of AI in cybersecurity. By understanding how AI can be used to create zero-day hacks, you can take steps to protect yourself and your organization.
- Use AI-powered security systems to detect and respond to threats.
- Stay up-to-date with the latest security patches and updates.
- Implement two-factor authentication to add an extra layer of security.
Concrete Example
For example, you can use AI-powered security systems like Google Cloud Security to protect your organization from security threats. These systems use machine learning algorithms to detect and respond to threats in real-time.
Or, you can use AI-powered tools like Python to develop your own security systems. Python is a popular programming language used for developing AI and machine learning models.